Month: August 2015
Open-source typeface “Hack” brings design to source code
The days of coders being shackled to Monaco or Courier New ends now. At SourceFoundry.org this week, programmer Chris Simpkins debuted the 2.0 version of Hack, an open-source typeface designed specifically for use in source code.
Hack is characterized by a large x-height, wide aperture, and low contrast design in order to be “highly legible” at common coding text sizes. Its “sweet spot runs in the 8px-12px range on modern desktop and laptop monitors,” Simpkins writes on GitHub. “Combine it with an HD monitor and you can comfortably work at 6 or 7px sizes.” As seen in the image above, there’s a heavier semi-bold weight in the regular font, and strategic serifs eliminate large gaps on each side of narrow characters. As Simpkins notes on the SourceFoundry site, this helps to distinguish glyphs like the lowercase l and number 1 at small text sizes.

Hack’s roots are in the libre, open source typeface community, and the project expands upon the contributions of the Bitstream Vera & DejaVu projects. (See a full contributors list here.) Simpkins has been working on the project throughout 2015, and he tweeted that this latest version includes “new open type features, changes in weights, significant changes in spacing, Powerline glyphs, and more.” The typeface now comes with four font styles: Regular, Bold, Oblique, and Bold Oblique.
Hack has been released as a free and open source project (available via SourceFoundry andGitHub) that is free to modify, to use in commercial situations, and to download for print, desktop, or Web. To display the typeface within its element, Sourcefoundry.org provides examples of Hack withinPython, C, and Javascript. There’s also a traditional font specimen available.
Source:http://arstechnica.com/
Ashley Madison: Two women explain how hack changed their lives
When infidelity dating site Ashley Madison was hacked, the details of 33 million user accounts were published on the web.
The BBC has spoken to two women, one whose fiance used the site and one who used it herself.
Neither wanted to be identified, but their stories give some hint of just how dramatic and wide-reaching the impact of the hack has been.
The first only wanted to be named as “Maria”. She says she used an online tool to search for her fiance’s email address in the dumped data.

“I really didn’t think I would find anything on anybody,” she comments.
She wanted to check, though, because one of her own email accounts had been compromised recently.
When she entered her fiance’s address as well, the database not only confirmed it was there but it spat back a postcode, city and birthdate. All were accurate.
“These things logged your IP [Internet Protocol] address, they logged your provider, they logged everything and not only that, it was your physical description,” she explained to the BBC. “It matched his to a T.”
Maria quickly confronted her fiance.
‘Multiple affairs’
“He denied and denied and denied at first and then he acquiesced and confessed what he did.
“Yes, (he said) he did have multiple affairs, yes. It just… it came out,” she says.
Her fiance said that he couldn’t explain fully why he did what he did and that Maria meant more to him than the women he had met on Ashley Madison. But the conversation didn’t last long.
Maria packed a week’s worth of clothes and left to stay with a friend. The wedding they had been planning is cancelled.
She has since booked a sexual health check, she says, and tried to distance herself as much as possible from her fiance. The whole experience has been “shattering”, she adds.
“It’s one thing if you come forward and say I’m not satisfied or I’m not happy or I’m finding it hard to remain faithful – as long as you’re open,” she says.
“It’s just completely unfair to waste years of a person’s life with duplicity.”
Online advice
You don’t have to look far online to find examples of internet users who seem to be personally affected by the hacking of Ashley Madison. Various forums are full of threads from those who believe their “SO” (significant other) was on the site.
But users of the dating site are also turning to the web for help.
One woman who used Ashley Madison, but who did not want to be named, has also spoken to the BBC. For the purposes of this article, we will refer to her as “Amy”.
She has been married to her husband for 10 years.
But recently she became interested in the idea of having an affair. She had heard advertisements for Ashley Madison on local radio, so a year ago she signed up and began looking for a man with whom to have a relationship.
However, she says she never messaged anyone and soon closed down the account. But six months ago she created another and this time she wanted to address questions she had about her sexuality by contacting other women.
This time she did find someone to talk to. They emailed one another, she says, for several weeks.

“She was close to where I live and we seemed to hit it off,” says Amy.
“Her story seemed so much similar to mine. She was someone who had been married for a while [and] she had always been curious about that side of herself.”
Amy says the woman she corresponded with told her she thought she was attractive, which made Amy feel flattered.
They were due to to meet, but at the last moment Amy called it off. She says she became fearful and began to feel that her marriage was something she didn’t want to jeopardise.
“Using it kind of made me realise that there were other things that I need to look at,” she explains.
“It’s scary when you have this person that you love so much and you think about hurting them.”
Married and curious
Amy says that so far she hasn’t told anyone who knows her about what happened, but she’s now worried that her husband might find out that she used the site.
She has distracted herself with work for now, but comments that she feels stressed and that the episode has affected her sleep.
Ashley Madison offered users a $19 (£12) “Full Delete” service, which Amy says she used. She checked an online tool to search for her email address in the leaked database and was surprised to find it there, along with other information such as her postcode, gender and the name associated with her credit card.
It’s not clear what has happened in this case, but it’s possible that the database was downloaded by hackers before the date on which Amy paid for her information to be removed.
Either way, she thinks there is now a possibility she’ll be found out.
“If my husband were to come home from work today and say someone found my information I would be open and honest with him about it,” she says.
“It’s really made me think about my behaviour and why I did what I did – and to cherish what I have.”
For now, though, Amy just hopes her husband won’t find out.
Source:http://www.bbc.com/
iOS Jailbreak Backdoor Tweak Compromised 220,000 iCloud Accounts
The recent security breach on iOS platform left 220,000 iCloud user accounts vulnerable due to a backdoor privacy attack caused by the installation of a malicious jailbreak tweak, according to an online Chinese vulnerability-reporting platform WooYun.
Yes, 220,000 is a huge number considering it happened to iOS, one of the most popular mobile operating system that is designed by Apple. But don’t get too frightened because this security flaw has nothing to do with Apple’s security and happened after a jailbreak attempt.

WooYun is a Chinese platform that reports on user submitted security flaws discovered by the researchers in an attempt to provide feedbacks to relevant vendors. So it is, in fact, a reliable website.
According to the post on their website, they have outlined the details about this backdoor attack that breached 220,000 iCloud accounts because of the installation of a malicious jailbreak tweak. In the page, they have also mentioned that the notification about the security flaw has already been issued to the appropriate vendors –apparently Apple.
Below is the (slightly broken) translated version of the report.
What should make the iCloud users worried is that if your account credentials are breached then it is surely going to have a negative impact as the leaked credentials grant an easy access to your personal information stored in the iCloud including all your photos and contacts.
Now you must be wondering that what the reason behind the flaw is. One of a Reddit user, self.jailbreak created a dedicated post about the issue where he outlined that the security breach affected the users in a specific region only and had abounded reach.
“THIS WAS ANNOUNCED BY A CHINA SECURITY WEBSITE WOOYUN (IT MEANS BLACK CLOUD IN CHINESE BASED ON SOUND) EARLIER ON THEIR WEIBO, AND IT IS BASICALLY TELLING THAT THERE ARE SOME SHADY TWEAKS THAT HAVE BACK-DOORS IS STEALING JAILBREAK USER’S ICLOUD ACCOUNT AND PASSWORD TO A REMOTE SERVER, WHICH SO FAR THERE ARE ROUGHLY 220 THOUSAND ACCOUNTS HAS BEEN LEAKED. THEY HAVEN’T ANNOUNCE THAT WHO STOLE IT AND WHAT FOR, BUT AS FAR AS WE KNOW THAT, IF THEY HACK INTO OUR ICLOUD ACCOUNTS, THEY CAN HAVE ACCESS TO OUR MAILS, PHOTOS OR EVEN PRIVATE STUFF.”
So considering how privacy conscious the iOS jailbreak community is and the tweaks and plug-ins released by them is secure, which makes it highly unlikely that a malicious jailbreak tweak would affect such a huge number of users, and that too by the installation of a single tweak or plug-in.
Here is the proof of the leaked iCloud account data, but apart from this picture, there is nothing else has been surfaced on the Internet yet!
One of the related Reddit users posted a valuable comment on the post that says:
“IN ASIAN COUNTRIES, IT IS VERY COMMON FOR PEOPLE TO BUY PHONES, NEW OR USED, FROM TECHNOLOGY MARKETS. AT THOSE MARKETS ARE LOTS OF COMPETING STALLS SELLING PHONES, AND JAILBREAKING YOUR PHONE AND SELLING IT TO YOU PREINSTALLED WITH LOTS OF JAILBROKEN / PIRATED APPS IS PART OF THEIR SERVICE.
THAT IS PART OF WHY JAILBREAKING / PANGU IS SO POPULAR IN ASIA / CHINA. THERE ARE ENTIRE MARKETS OF CHINESE-ONLY PROGRAMS AND APPS THAT WE ARE NOT REALLY EXPOSED TO HERE ON THIS ENGLISH- / WESTERN-DOMINATED SUBREDDIT.
ANYWAY, MY POINT IS THAT IF ONE OF THESE “SHADY” APPS IS SOMETHING THAT WAS SOMEWHAT COMMON FOR THESE 3RD-PARTY SELLERS TO INSTALL, THEN THIS STAT WOULDN’T BE THAT SURPRISING. IT DOESN’T TAKE 220,000 PEOPLE WITH PERSONAL TECH KNOW-HOW TO JAILBREAK AND DOWNLOAD A TWEAK: IT JUST TAKES 220,000 PEOPLE BUYING FROM A FEW HUNDRED / THOUSAND TECHNOLOGY BOUTIQUE SHOPS THAT PRELOAD THE SOFTWARE.”
He did raise a valuable point here that it seems like this attack is caused by the installation of malicious tweaks and plug-ins by the third-party sellers, and then the users used those infected devices resulting in a breach of their accounts.
HOW CAN YOU PROTECT YOUR ICLOUD ACCOUNT?
We all know that jailbreaking your iOS device makes it vulnerable to malicious attacks resulting in an increased risk. To protect yourself from these malicious attacks, it is recommended you to take the following precautionary steps:
Tip #1 – Enable two-factor authentication on your iCloud account.
Tip #2 – Don’t download tweaks from any untrusted or third party repository.
Tip #3 – Stay away from pirated apps or tweaks.
But still, even after following the above-mentioned tips you might be vulnerable to security threats because a jailbroken device is never secure!
Source:https://www.hackread.com
How to hide secret messages in music files?
There are many reasons to hide information but most common reason is to protect it from unauthorized access and people coming to know the existence of the secret information. In the corporate world audio data hiding can be used to hide and secure confidential chemical formulas or designs of new invention. Not only in commercial sector, it can also be used in used in the non-commercial sector to hide data that someone wants to keep private. Terrorists organization have been using audio data hiding since long time to keep their communications secret and to organize attacks. We are going to talk about confidential information hiding with the help of information and data security solutions expert.
Steganography is the science of hiding confidential information in a cover file so that only dispatcher and recipient know the existence of the confidential information. Confidential information is encoded in a way so that the very existence of the information is hidden. The main objective of steganography is to converse securely in a completely invisible mode and to shun drawing doubt to the communication of hidden information. Steganography not only prevents people from knowing about the hidden confidential information, but it also prevents others from thinking that somebody is communicating in a hidden way. If a steganography technique causes someone to believe there is hidden information in a carrier medium, then the technique has botched. The essential technique of audio steganography consists of Carrier (Audio file), Message and Password. Carrier file is also called as a cover-file, which hides the confidential information. Essentially, in steganography message is the information that the sender desires that it should remain confidential. Message can be image, plain text, audio or any type of file. Password is also called as a stego-key, and it assures that only the receiver who knows the password will be able to extract the confidential information or message from a cover-file. The cover-file with the confidential information is called as a stego-file.
The confidential information hiding procedure consists of subsequent two steps:
- Identification of redundant bits in the cover-file. Redundant bits are that bits that can he modified without corrupting the eminence or destroying the integrity of the cover-file.
- To insert the confidential information in the cover file, the redundant bits in the cover file is interchanged by the bits of the confidential information.
AUDIO STEGANOGRAPHIC METHODS
Mike Stevens, information and data security training explains that there have been many approaches for hiding confidential information or messages in audio in such a manner that the changes made to the audio file are not visible. Common approaches are:
LSB CODING
LSB (Least Significant Bit) approach is very famous approach and it replaces the least significant bit in some bytes of the cover file to conceal a sequence of bytes enclosing the hidden data. That’s usually an effective approach in cases where the LSB substitution doesn’t cause significant quality degradation, such as in 24-bit bitmaps. In computing, the least significant bit (LSB) is the bit position in a binary integer contributing the unit’s value, that is, controlling whether the number is even or odd. Using this approach you can hide a byte every eight bytes of the cover. There’s a fifty percent chance that the bit you’re substituting is the same as its replacement, in other words, half the time, the bit doesn’t change, which helps to reduce quality degradation.
PARITY CODING
Parity coding is one of the most robust audio steganographic approach. In place of breaking a signal into individual samples, this approach breaks a signal into separate samples and inserts each bit of the confidential information from a parity bit. If the parity bit of a chosen region does not match the secret bit to be encoded, the procedure inverts the LSB of one of the samples in the region. Hence, the sender has different choices in encoding the secret bit.
PHASE CODING
The phase coding method works by switching the phase of an initial audio segment with a reference phase that symbolizes the confidential information. The persisting segments phase is changed in order to preserve the relative phase amid segments. In terms of signal to noise ratio, Phase coding is very effective coding approach. When there is a drastic change in the phase relation amid each frequency element, noticeable phase dispersion will happen. But, as long as the alteration of the phase is adequately small, an inaudible coding can be attained. This approach relies on the fact that the phase elements of sound are not as perceptible to the human ear as noise is says ethical hacking training professor.
SPREAD SPECTRUM
The basic spread spectrum (SS) approach tries to spread confidential information through the frequency spectrum of the audio signal. This is like system, which uses logic of the LSB that spans the message bits unsystematically over the complete sound file. Nevertheless, dissimilar to LSB coding, the Spread Spectrum approach spreads the confidential information through the frequency spectrum of the sound file using a code, which is sovereign of the actual signal. Thus, the final signal captures a bandwidth, which is more than what is actually needed for transmission.
ECHO HIDING
Echo hiding procedure inserts confidential information in a sound file by presenting an echo into the discrete signal. Echo hiding has benefits of delivering a high data transmission rate and higher robustness when competed to other methods. Only one bit of confidential information could be encoded if only one echo was created from the original signal. Therefore, before the encoding procedure begins the original signal is broken down into blocks. When the encoding procedure is done, the blocks are concatenated back together to deliver the final signal.
With the help ofAs per ethical hacking training organization professor of IICyberSecurity, we are going to see some software and mobile apps, which people can use to encode their messages and send hidden messages via email, social media or WhatsApp mobile phone.
DeepSound
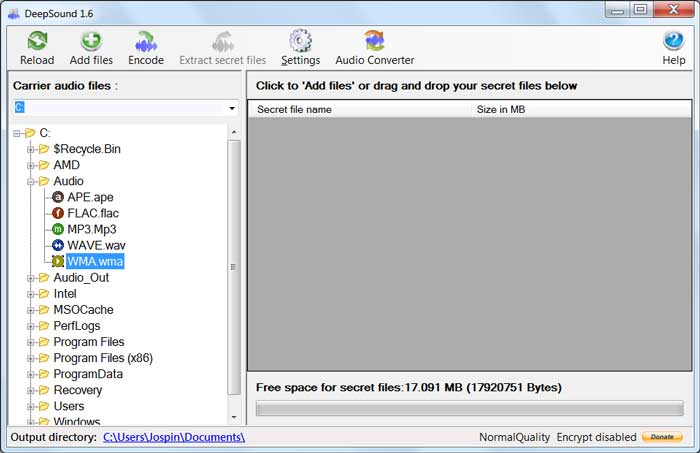
Deep sound is audio stenography software for windows and can be use to create secret message via audio file. It is information security solutions freeware and supports all kinds of audio files.
Hide secret information into carrier audio file
To hide secret information into audio file, do the following steps:
- Choose the carrier audio file and make sureits format is one of them flac, wav, wma, mp3, ape.
- Click encode and the file will be encoded and then you can click ‘Add files’ to add secret files into the panel on the right side of application.
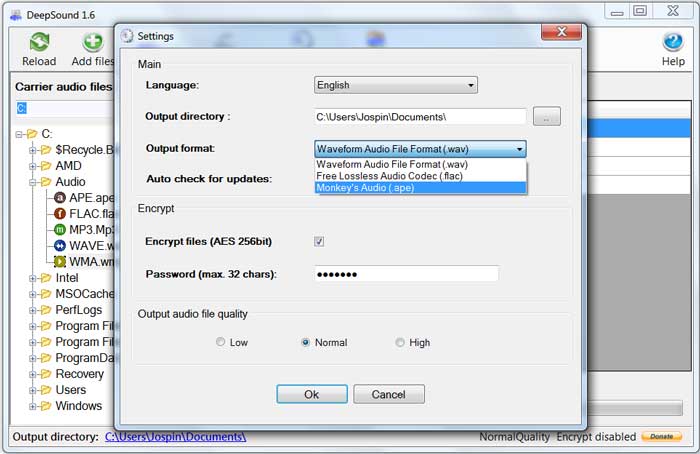
- You can choose output audio format (wav, flac or ape). DeepSound does not support wma output format. If you desire to hide secret information into wma, hide secret information into wav file and then use external software such as Windows Media Encoder for change wav to wma lossless.
- In the settings you can select to turn On/Off encrypting and set password. New audio file will be saved to the output directory. Select Ok to start hiding secret files into carrier audio file.
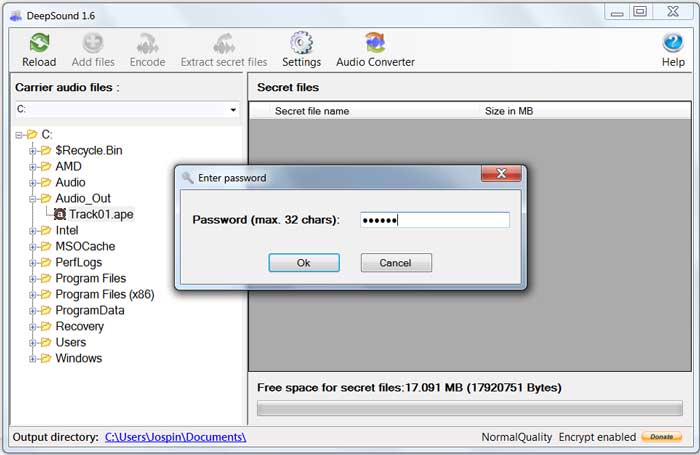
Extract secret data from audio file
As per information and data security solutions experts, to remove secret data from audio file, follow the following steps:
- In the file explorer, choose the audio file, which encloses secret data. If the secret files are encrypted, input password.
- DeepSound examines the selected file and exhibits secret files. Click the right mouse button and press F4 key or select extract secret files.
How to convert audio files
Open Audio Converter
To add input files select ‘Add files’ button and the supported input audio formats are:
– Waveform Audio File Format (.wav)
– Free Lossless Audio Codec (.flac)
– Windows media audio lossless (.wma)
– MPEG audio layer-3 (.mp3)
– Monkey’s Audio (.ape)
Choose Output Format for the file and the supported output audio formats are:
– Waveform Audio File Format (.wav)
– Free Lossless Audio Codec (.flac)
– MPEG audio layer-3 (.mp3)
– Monkey’s Audio (.ape)
You can learn more about DeepSound en information security training of International Institute of Cyber Security.
Hide It In
This app conceals an image taken with your iPhone camera into another apparently innocuous image from your photo library. Select the cover image and take any photo from your mobile phone. You can hide It In characters among other things, AES encryption to safeguard that even if the existence of a secret message is questioned, only the people with password can recover the hidden image.
Acostic Picture Transmitter
This app lets you transfer and accept images acoustically. To do this each column of the selected message gets altered by a Fast Fourier Transform and outputted across iPhones speaker. On the accepting iOS-device the received audio is envisioned by a spectrogram and the arriving images become visible. You can use this app for instance to transfer images very effortlessly over a phone or to put images in all kind of audio recording says information security solutions experts.
Steg-O-Matic
According to developer BlueJava, the Steg-O-Matic app hides the secret message in an image and offers tools for sending the image via email, social media or post it on a public blog. Only those intended to read the secret will know to look for it and know how to retrieve it. You can learn more about it doing information security training.
DaVinci Secret Message
An Android app, DaVinci Secret Message can password shield the data hidden within an image, providing another level of security. It also provides the choice to delimit the size of the final image, thus making it more challenging to suspect whether a carrier image holds a secret based on its size alteration from the original image file.
Incognito
This Android application uses both steganography and cryptography to hide diverse types of data such as text messages, pdf files, images, music files, etc. within images without altering the superficial appearance of the image. The experts of ethical hacking training endorses it for use by business individuals worried about competitors spying.
Source:http://www.iicybersecurity.com/audio-steganography.html
Court Says the FTC Can Slap Companies for Getting Hacked
FOR COMPANIES LIKE the dating site Ashley Madison or the health insurer Anthem, financial loss, customer anger and professional embarrassment aren’t the only consequences of getting massively gutted by hackers. Now a court has confirmed that there’s a three-letter agency that can dish out punishment, too.
In a decision published Monday, a U.S. appellate court ruled that the Federal Trade Commission has the authority to sue Wyndham Hotels for allowing hackers to steal more than 600,000 customers’ data from its computer systems in 2008 and 2009, leading to more than $10 million in fraudulent charges. The ruling more widely cements the agency’s power to regulate and fine firms that lose consumer data to hackers, if the companies engaged in what the FTC deems “unfair” or “deceptive” business practices. At a time when ever-more-private data is constantly getting breached, the decision affirms the FTC’s role as a digital watchdog with actual teeth.
‘This Is a Major Deal’
The FTC originally sued Wyndham in 2012 over the lack of security that led to its massive hack. But before the case proceeded, Wyndham appealed to a higher court to dismiss it, arguing that the FTC didn’t have the authority to punish the hotel chain for its breach. The third circuit court’s new decision spells out that Wyndham’s breach is exactly the sort of “unfair or deceptive business practice” the FTC is empowered to stop, sending Wyndham back to face the FTC’s lawsuit in a lower court.

“A company does not act equitably when it publishes a privacy policy to attract customers who are concerned about data privacy, fails to make good on that promise by investing inadequate resources in cybersecurity, exposes its unsuspecting customers to substantial financial injury, and retains the profits of their business,” reads the court’s ruling.
For consumer privacy watchdogs, the ruling comes as a relief, solidifying another serious legal incentive for companies to invest in protecting their customers’ data, according to Electronic Privacy Information Center attorney Alan Butler. “This a huge victory for the FTC, but also for American consumers,” says Butler, who filed an amicus brief defending the FTC’s authority earlier in the case. “We see services and companies being hacked on an almost daily basis now. Having the FTC out there, bringing actions against companies that fail to protect consumers’ data is a critical tool.”
Wyndham Hotels, for its part, vowed to continue its case in the lower court. The company points out that the appellate court ruled on the FTC’s authority, not the specific allegations the agency made against Wyndham, namely that it had failed to adequately protect its customers. “We believe the facts will show the FTC’s allegations are unfounded,” reads a statement from Wyndham spokesperson Michael Valentino. “Safeguarding personal information remains a top priority for our company, and with the dramatic increase in the number and severity of cyberattacks on both public and private institutions, we believe consumers will be best served by the government and businesses working together collaboratively rather than as adversaries.”
Even if Wyndham does eventually lose its case against the FTC, it likely won’t be fined, says Berkeley Law professor Chris Hofnagle. Instead, it could face the kind of privacy probation that is a frequent outcome of the FTC’s privacy suits against firms, in which the agency closely oversees its data protection systems for a period as long as 20 years, with the option to later impose fines for any violation of the standards it imposes.
But aside from Wyndham itself, the appellate ruling establishes a more important precedent for the legal consequences of a data breach. “Had Wyndham won at the third circuit, it would have called into question the FTC’s ability to police privacy and security,” says Hofnagle, describing that avoided outcome as a “disaster” for the agency. “This is a major deal.”
Data Insecurity As ‘Unfair’ Business Practice
In its original lawsuit, the FTC accused Wyndham of a long litany of privacy fails, from storing credit card information unencrypted to lacking firewalls to using easily-guessed passwords. The agency compared those practices to Wyndham’s published privacy policy—which promised that it did use some kinds of encryption to protect consumer data as well as firewalls and other “safeguards”—and argued that its insecurity amounted to “unfair” business practices.
Wyndham had specifically challenged that “unfair” claim, arguing that it hadn’t actually engaged in the “unscrupulous or unethical behavior” that it said the FTC’s standard requires. But the appellate court wasn’t persuaded; It ruled that the alleged mismatches between its data protection and its privacy policy were sufficient to meet that “unfair” standard, without any accusations of “unethical” behavior necessary.
The Court also rejected another argument from Wyndham that if the FTC were allowed to punish companies for this sort of data breach, it would be allowed to sue any supermarket that’s “sloppy about sweeping up banana peels,” opening the door to unfair practice claims run amok. On that point, the Court snapped back: “Were Wyndham a supermarket, leaving so many banana peels all over the place that 619,000 customers fall hardly suggests it should be immune from liability.”
The appellate ruling doesn’t necessarily grant the FTC new powers so much as dispel legal questions around the power it already possesses to be a data security watchdog, says Berkeley’s Hofnagle. As data breaches increasingly become a source of real suffering for consumers—see the reports of suicides that have already resulted from Ashley Madison’s scandalous data spill—the agency’s mandate more important than ever.
“The law has always imposed responsibility on companies for the care of their customers. When you’re in the restaurant you have to be protected against slips and falls or food-borne illness,” says Hofnagle. “Data is just something new that companies have to protect if they want to bear the benefits of collecting it.”
Source:http://www.wired.com/
Telstra News spews banking trojan after malvertising attack
Australia’s dominant telco, Telstra, has been serving one of the world’s most dangerous hacking tools after its news site was infected with malvertising.
Malwarebytes researcher Jerome Segura says the attackers were likely dropping the Tinba trojan, considered to be the world’s smallest malware by file size at about 20kb and one that raids bank accounts.

“The media home page of Australia’s largest telecommunications company, Telstra, was pushing some malvertising similar to the attack we just documented on the PlentyOfFish website,” Segura says.
It is unknown and difficult to know how many if any users have been popped, but the best exploit kits like Nuclear compromise up to 40 percent of users who encounter it.
Attackers had compromised the media.telstra.com.au/home website through a malicious advertisement. That ad redirects visitors through Google’s URL shortener to a website hosting the Nuclear exploit kit.
The attack is not a hack of the Telstra asset but rather a compromise of the advertising chain through which criminals swindle advertising networks like Google and Yahoo!.
The Nuclear exploit kit is the second most popular off-the-shelf hacking box behind the Angler exploit kit. It contains the latest vulnerabilities for runtime environments like Adobe Flash and for browsers such as Internet Explorer.
Net scum use these kits to speed up and improve the delivery of payloads such as Tinba.
Source:http://www.theregister.co.uk/
Apple users are vulnerable to sandbox vulnerability
Experts discovered that the sandbox vulnerability affects all apps that use the managed app configuration setting in devices that run older versions.
Kevin Watkins, a security researcher from Appthority, argues that users without iOS 8.4.1 are affected by the sandbox vulnerability, CVE-2015-3269. The flaw affects all apps that use the managed app configuration settings, meaning that Apple is storing enterprise credentials in a directory that can be read by everyone.

“IT will commonly send the credential and authentication information along with the managed app binary for installation on corporate mobile devices [which] often included access to the corporate data security jewels, including server URLs, and credentials with plaintext passwords,”.
“The underlying issue with our critical sandbox violation discovery is that … anyone can also see the credential information on the mobile device as it is stored world readable.” said Watkins.
“An attacker could target as many enterprises it can get into (using the iTunes store to spread an app designed to read and share the configuration files), or a specific target (traditional spear-phishing attack, through targeted e-mail, etc). In either case, they would develop an app that has a high chance of being installed in the enterprise, such as a productivity app. Once the app gets downloaded and installed on the devices, it would continuously monitor the directory for configuration settings being written to the world readable directory, harvesting and sending them to the attacker. Because all apps have access to the directory, it could hide in plain sight and operate as one of the many legitimate apps that have access to the directory in question.”
“An attacker (or a malicious app) with access to an MDM managed device can read all managed configuration settings for an unpatched device. Managed configuration is used to make the provisioning of apps easier and enterprise apps may use this mechanism to provision credentials or details about internal infrastructure this way. Those can be used by the attacker to gain access to those services.”
Corporate app data are more exposed, the expert highlighted the risk of a cyber attack that canallow hackers to steal information stored in an open directory (including mobile device management).
The tests conducted by Watkins revealed that medical apps used by doctors were leaking patient data, user names, passwords, authentication tokens.
“We also found apps used in the healthcare industry, giving doctors access to patient data and records (a likely HIPAA violation).” continues Watkins.
The analysis of the managed settings used by these apps revealed:
- Close to half (47%) referenced credentials, including username, password and authentication tokens.
- 67% referenced server identification information.
The good news is that Apple patched the CVE-2015-3269 sandbox vulnerability with the release iOS 8.4.1, but yet many people are running older iOS versions. It has been estimated that around 70% of users still have older iOS versions and still taking some months until iOS 8.4.1 is fully spread.
Please keep in mind the following recommendations to avoid these type of problems:
- Not using this mechanism to provision secret / confidential data
- Credentials and other secrets should always be stored using the device keychain
- A possible way to provision this data would be to use url schemes
- Use iOS single-sign-on profiles if possible
Elsio Pinto (@high54security) is at the moment the Lead Mcafee Security Engineer at Swiss Re, but he also as knowledge in the areas of malware research, forensics, ethical hacking. He had previous experiences in major institutions being the European Parliament one of them. He is a security enthusiast and tries his best to pass his knowledge. He also owns his own blog Mcafee Security Engineer at Swiss Re, but he also as knowledge in the areas of malware research, forensics, ethical hacking. He had previous experiences in major institutions being the European Parliament one of them. He is a security enthusiast and tries his best to pass his knowledge.
Source:http://securityaffairs.co/
Anonymous Hacks South African Government Contractor for OpMonsanto
Remember the Anonymous hackers behind the massive World Trade Center (WTC) leak? Well, they are back with another breach.
The online hacktivist Anonymoushas changed its direction from the American soil to once the land of diamonds South Africa. The reason behind the sudden change is Internet censorship and Monsanto’s dominance in the country.

Anonymous conducted the attack under the banner of #OperationSA and #OpMonsanto in which the prime target of the attack was South African government contractor IT company’s subsidiaries “State Information Technology Agency (SITA).”
SITA suffered a massive breach on 12th August in which Anonymous accessed its online servers and leaked a trove of confidential data over the Internet.
The leaked data has been divided in four parts and contains database of the SITA’s website, records such as full names, usernames, emails along with their clear-text and encrypted passwords, addresses, phone and fax numbers of the officials and registered users of the site.
The last folder of the data contains emails, full names and phone numbers of the South African government officials including the parliamentarians.
 After scanning the data, we have found it to be legit and never been leaked online in the past.
After scanning the data, we have found it to be legit and never been leaked online in the past.
In an exclusive conversation with one of the Anonymous hackers behind the breach, HackRead was told that SITA was attacked due to its importance in the country and data was leaked with the intention of raising voice against human rights abuses and dominance of the Monsanto company in South Africa.
According to Anonymous,
“WE WILL FIGHT MONSANTO AND ITS POISONOUS FOOD PRODUCTS. WE WANT TO MAKE SURE THE SOUTH AFRICAN PEOPLE ARE NOT ALONE IN THIS WAR AGAINST HUMAN RIGHTS ABUSES AND INTERNET CENSORSHIP LAWS.”
The Anonymous hacker behind this attack previously hacked two major Israeli arms dealers/importers and leaked thousands of client login data online.
Source:https://www.hackread.com
Hacker pleads guilty in Facebook malware and spam scheme
A New York man has pleaded guilty in federal court for violating an anti-spam law, although his alleged involvement in cybercriminal activities went way beyond sending spam.
Eric L. Crocker, the accused hacker, pleaded guilty to just one charge carrying a maximum penalty under the CAN-SPAM Act of three years in prison and a fine of $250,000.
Crocker was allegedly involved in hacking computers to create an enormous botnet that he maintained for co-conspirators, who used the network of compromised computers to send spam and much more.

Crocker was one of a dozen people arrested in the US in July for their connection with the notorious Darkode cybercrime forum.
According to US Attorney David J. Hickton, of the Western District of Pennsylvania, Crocker used Darkode to market his botnet.
An unidentified co-conspirator paid Crocker and others $200-$300 for every 10,000 computers they infected as part of the botnet, according to the federal indictment.
To build the botnet, Crocker infected victims through Facebook.
As described by law enforcement, Crocker used a “Facebook Spreader” malware called Slenfbot to infect victims via booby-trapped links in Facebook chat messages.
It worked like this: a user became infected after clicking on a link to the malware sent to them via a Facebook message. The malware was then used to send phishing messages to the victim’s friends on the social network.
When those recipients clicked on a link in the message, thinking it was from their friend, they automatically downloaded the malware and so the cycle began again.
Once the malware was on a victim’s computer, the computer became a “bot” that Crocker could control remotely to send further spam.
The Darkode forum, where Crocker allegedly sold his services as “Phastman,” was taken down by the FBI and Europol in July 2015.
Described by the FBI as “the most sophisticated English-speaking forum for criminal computer hackers around the world,” Darkode’s small membership used it as a hub for buying and selling services including malware, zero-day exploits, and botnets.
Members reportedly included some of the Lizard Squad hackers responsible for denial-of-service attacks on Sony and Microsoft.
Como crack aplicación de iOS App store
Podemos crack cualquier aplicación en nuestro dispositivo iOS con la ayuda de este software. Todas las aplicaciones descargadas de la App Store se guardan en /var/mobile/Applications/ y se almacenan en forma encriptado acuerdo con los profesionales de empresa de seguridad informática en México. Tendremos que descifrar estas aplicaciones para hacer el análisis de ellas. Podemos descifrar las aplicaciones con la ayuda de Clutch o Rasticrac.
Clutch funciona con la mayoría de las aplicaciones y el bueno de clutch es que podemos configurar los valores de configuración de acceso a través de la MobileTerminal. Cluch puede hacer crack de la mayoría de todas las aplicaciones ARMv7 con facilidad explica maestro de curso de hacking ético. En terminal escriba el siguiente comando
Clutch Esto ahora enumerar todas las aplicaciones cifradas que están instaladas en su dispositivo, seleccione la aplicación que desea a crack y escribe el siguiente comando Clutch “Nombre de aplicación” Clutch ahora comenzará a hacer cracking de la aplicación elegida / s, y una vez hecho, le dirá y volver a la línea de comandos. La aplicación agrietada se colocan en
/var/root/Documents/Cracked o /User/Documents/Cracked
Pueden entender con más detalle en el entretenimiento de hacking ético de qué hacer con la aplicación agrietada y cómo mudar la aplicación en AppAddict. Si usted va a hacer cracking de muchas aplicaciones, sería una buena idea para personalizar sus herramientas de cracking ligeramente y haga que su nombre añade al nombre del archivo según consejos de expertos de seguridad de la nube en México. También podemos hacer que lo que un expediente de crédito secreta se coloca dentro de la aplicación con su nombre, esto es lo que las personas no pueden robar su trabajo. Vaya a la siguiente carpeta de su dispositivo
/etc Allí podrá ver un archivo llamado “clutch.conf” abre este archivo con su editor y modifica los siguientes dependiendo de lo que quieras.
CreditFile no (Cambio en Yes para crear archivos de crédito dentro de la aplicación) FilenameCredit no (Cambio en YES para agregar el nombre de Cracker a nombre del archivo) CrackerName (Ingrese su nombre Cracker entre medio) ListWithDisplayName Sí (Cambiar al directorio a la lista de aplicaciones en forma completa dentro del menú de Cracker) MetadataEmail (Puede cambiar cualquier dirección de correo electrónico)
Rasticrac
Rasticrac es uno de los más poderosos utilidad de cracking y su fácil de usar y funcionalidades es mejor que el Clutch según recomendación de curso de hacking ético y seguridad informática en México. Rasticrac es una versión actualizada de la herramienta PCM Cracking (PoedCrackMod). Rastcrac se ejecuta en todos los dispositivos iOS.

Como crack aplicación de iOS App store
En su terminal escriba el siguiente comando
rasticrac -m Esto ahora mostrará una lista de todas las aplicaciones cifradas que están instalados en el dispositivo, aparecerá una lista de la aplicación con un número, letra o combinación de ambos en el lado dependiendo del número de aplicaciones que ha instalado. Escribe App /s junto con que el número o símbolo de la aplicación que desea crack menciono el experto de empresa de seguridad informática. Rasticrac ahora comenzará a trabajar en crack la app / s que ha elegido. La aplicación agrietada se colocan en
/var/root/Documents/Cracked
Vaya a la siguiente ubicación de su dispositivo /usr/bin Allí podrá ver un archivo llamado “rasticrac” abrir este archivo con el editor de texto y modifique los siguientes dependiendo de lo que quieras
# – CrackerName defecto (o “Anónimo”). RCcracker = “Anónimo” (Cambiar a su nombre de Cracker) # – En caso de “detalles extra” aparecerá en el nombre Ipa (es decir: “iPad / 3GS / etc) RCextras = “YES” (Cambiar a NO si no desea información adicional se suma a los nombres de los archivos de las aplicaciones Según Jim Taylor experto de servicios de seguridad en la nube) # – Si la escritura hablar con usted? (que sólo habla Inglés, sólo que con iOS4 +, solamente con “hablar” herramienta desde Cydia) RCspeak = “YES” (Cambiar a NO para apagar la voz) # – Si el nombre del artista puede utilizar en el nombre de archivo? RCartistfrommeta = “YES” (Cambiar a NO si no desea que el nombre desarrolladores en sus aplicaciones agrega el nombre de archivo)
Hackers Finally Post Stolen Ashley Madison Data
HACKERS WHO STOLE sensitive customer information from the cheating site AshleyMadison.com appear to have made good on their threat to post the data online.
A data dump, 9.7 gigabytes in size, was posted on Tuesday to the dark web using an Onion address accessible only through the Tor browser. The files appear to include account details and log-ins for some 32 million users of the social networking site, touted as the premier site for married individuals seeking partners for affairs. Seven years worth of credit card and other payment transaction details are also part of the dump, going back to 2007. The data, which amounts to millions of payment transactions, includes names, street address, email address and amount paid, but not credit card numbers; instead it includes four digits for each transaction that may be the last four digits of the credit card or simply a transaction ID unique to each charge. AshleyMadison.com claimed to have nearly 40 million users at the time of the breach about a month ago, all apparently in the market for clandestine hookups.
“Ashley Madison is the most famous name in infidelity and married dating,” the site asserts on its homepage. “Have an Affair today on Ashley Madison. Thousands of cheating wives and cheating husbands signup everyday looking for an affair…. With Our affair guarantee package we guarantee you will find the perfect affair partner.”
The data released by the hackers includes names, addresses and phone numbers submitted by users of the site, though it’s unclear if members provided legitimate details. A sampling of the data indicates that users likely provided random numbers and addresses, but files containing credit card transactions will yield real names and addresses, unless members of the site used anonymous pre-paid cards. One analysis of email addresses found in the data dump also shows that some 15,000 are .mil. or .gov addresses.
The data also includes descriptions of what members were seeking. “I’m looking for someone who isn’t happy at home or just bored and looking for some excitement,” wrote one member who provided an address in Ottawa and the name and phone number of someone who works for the Customs and Immigration Union in Canada. “I love it when I’m called and told I have 15 minutes to get to someplace where I’ll be greeted at the door with a surprise—maybe lingerie, nakedness. I like to ravish and be ravished … I like lots of foreplay and stamina, fun, discretion, oral, even willingness to experiment—*smile*”
Passwords released in the data dump appear to have been hashed using thebcrypt algorithm for PHP, but Robert Graham, CEO of Erratasec, says that despite this being one of the most secure ways to store passwords, “hackers are still likely to be able to ‘crack’ many of these hashes in order to discover the account holder’s original password.” If the accounts are still online, this means hackers will be able to grab any private correspondence associated with the account.
It’s notable, however, that the cheating site, in using the secure hashing algorithm, surpassed many other victims of breaches we’ve seen over the years who never bothered to encrypt customer passwords.
“We’re so used to seeing cleartext and MD5 hashes,” Graham says. “It’s refreshing to see bcrypt actually being used.”
Here’s how the hackers introduced the new data dump:
Following the intrusion last month, the hackers, who called themselves the Impact Team, demanded that Avid Life Media, owner of AshleyMadison.com and its companion site Established Men, take down the two sites. EstablishedMen.com promises to connect beautiful young women with rich sugar daddies “to fulfill their lifestyle needs.” The hackers didn’t target CougarLife, a sister site run by ALM that promises to connect older women with younger men.
“Avid Life Media has been instructed to take Ashley Madison and Established Men offline permanently in all forms, or we will release all customer records, including profiles with all the customers’ secret sexual fantasies and matching credit card transactions, real names and addresses, and employee documents and emails,” the hackers wrote in a statement following the breach.
To show they meant business, they posted sample files containing some of the stolen data, which included company financial information detailing employee salaries and documents mapping the company’s internal network.
The hackers appeared to target AshleyMadison and EstablishedMen over the questionable morals they condoned and encouraged, but they also took issue with what they considered ALM’s fraudulent business practices. Despite promising customers to delete their user data from the site for a $19 fee, the company actually retained the data on ALM’s servers, the hackers claimed. “Too bad for those men, they’re cheating dirtbags and deserve no such discretion,” the hackers wrote. “Too bad for ALM, you promised secrecy but didn’t deliver.”
Avid Life Media defiantly ignored the warnings and kept both sites online after the breach, promising customers that it had increased the security of its networks.
That wouldn’t matter for the customers whose data had already been taken. Any increased security would be too little too late for them. Now they face the greatest fallout from the breach: public embarrassment, the wrath of angry partners who may have been victims of their cheating, possible blackmail and potential fraud from anyone who may now use the personal data and bank card information exposed in the data dump.
“Avid Life Media has failed to take down Ashley Madison and Established Men,” Impact Team wrote in a statement accompanying the online dump Tuesday. “We have explained the fraud, deceit, and stupidity of ALM and their members. Now everyone gets to see their data…. Keep in mind the site is a scam with thousands of fake female profiles. See ashley madison fake profile lawsuit; 90-95% of actual users are male. Chances are your man signed up on the world’s biggest affair site, but never had one. He just tried to. If that distinction matters.”
The hackers deflected responsibility for any damages or repercussions that victims of the breach and data dump may suffer.
“Find yourself in here? It was ALM that failed you and lied to you. Prosecute them and claim damages. Then move on with your life. Learn your lesson and make amends. Embarrassing now, but you’ll get over it,” they wrote.
It’s important to note that Ashley Madison’s sign-up process does not require verification of an email address to set up an account, so legitimate addresses might have been hijacked and used by some members of the site. One email in the data dump, for example, appears to belong to former UK Prime Minister (Tony Blair).
Avid Life Media condemned the release of the data.
“This event is not an act of hacktivism, it is an act of criminality. It is an illegal action against the individual members of AshleyMadison.com, as well as any freethinking people who choose to engage in fully lawful online activities,” the company said in a statement. “The criminal, or criminals, involved in this act have appointed themselves as the moral judge, juror, and executioner, seeing fit to impose a personal notion of virtue on all of society. We will not sit idly by and allow these thieves to force their personal ideology on citizens around the world.”
Source:http://www.wired.com/
Ransomware goes OPEN SOURCE in the name of education
Turkish security bod Utku Sen has published what appears to be the first open source ransomware that anyone can download and spread.
The “Hidden Tear” ransomware, available to GitHub, is a functional version of the malware the world has come to hate; it uses AES encryption to lock down files and can display a scare warning or ransom message to get users to pay up.
Sen says the malware will evade detection by all common anti-virus platforms.
“While this may be helpful for some, there are significant risks,” Sen says.
“Hidden Tear may be used only for educational purposes. Do not use it as a ransomware.”

One could envisage such “educational purposes” as entailing making the case for better backup systems for purse-holding superiors, but it is likely a hard case to state.
Github moderators will no doubt evaluate that claim. The site has not, at the time of writing, killed off the repository which may skirt the edges of its terms of service.
The malware is not nearly as slick as Cryptowall or Cryptolocker which sport unique Tor hidden service Bitcoin payment domains and have become a scourge of the internet in recent years.
In a video set to whimsical classical music, Sen demonstrates how the ransomware can encrypt and decrypt files leaving a text document note on the victim’s desktop.
It can encrypt a variety of files including word processor documents, spreadsheets, and Powerpoint.
Punters will need to have a web server capable of supporting scripting languages if they wish to test out the ransomware, Sen says.
Hackers Can Replace Apps on Your Android Device with New Vulnerability
The Zero-day vulnerability presented by IBM’s researchers Or Peles and Roee Hay will affect all Android devices.
The two researchers from IBM’s X-Force Application Security Research Team presented a paper titled One Class to Rule Them Allat the USENIX WOOT 2015 Security Conference held in Washington D.C.
In their paper, the researcher duo provided CVE-2014-3153 proof of concept. CVE-2014-3153 is a vulnerability that was identified by them in Android’s Open SSLX509 Certificate class.

The class, if and when leveraged by an attacker/hacker, would let them enhance the privileges of a lower-level app by allowing it super-privileges such as system user status on the android device.
HACKERS CAN REPLACE REAL APPS WITH FAKE ONES:
The CVE-2014-3153 zero-day vulnerability can easily be exploited by attackers as all they need is an entry point into the Android device. That is because they just need to inject a tiny snippet of code to enhance the privileges of an app. That tiny piece of code could be hidden in any low-level app or a game they would like. They may also host it on Play Store.
When the code is accessed and installed by a user, it will be executed and the low-level app would receive system-level privileges.
On the contrary, if the entry point is a “malicious” app and along with the escalation code, it contains additional complex procedures too then the user might get into greater trouble.
This vulnerability could easily be used by an attacker to install malicious APKs on any targeted android device. Later, the attacker could use them to replace authentic apps such as Facebook.
THE AFTERMATH:
Escalating privileges through this new zero-day vulnerability aren’t limited to replacing real apps with fake ones. Attackers can download just about anything they want to from the device as well as spy on the user. The user would never be notified or prompted with any popups about whatever is happening in the background.
AROUND 55% OF ALL ANDROID DEVICES TO BE AFFECTED:
Researchers claim that Android devices running the versions between 4.3 and 5.1 will get affected from this vulnerability. This means Jelly Bean, KitKat and Lollipop all will be affected. Moreover, the yet unnamed M version is vulnerable as well. This means around 55% of the Android market is in danger.
The IBM team also took steps to disclose this vulnerability properly and Google has issued patches already.
Source:https://www.hackread.com
Salesforce Patches XSS on a Subdomain
Salesforce.com has patched a vulnerability on one of its subdomains that exposed users to account takeover, phishing attacks and the installation of malicious code.
The vulnerability was disclosed yesterday by researcher Aditya K. Sood of Elastica Cloud Threat Labs.
Sood said admin.salesforce.com was vulnerable to a cross-site scripting attack that has since been patched after it was reported more than a month ago. Salesforce, Sood wrote in a blogpost, said the vulnerability posed less of a risk because it was present in a Salesforce subdomain.

“The vulnerability was not present in ‘login.salesforce.com,’ but in another subdomain of Salesforce. However, since the primary domain is ‘salesforce.com,’ this trust can be exploited through phishing attacks by tricking users into providing their legitimate credentials,” Sood said.
Sood said that Salesforce accounts for its applications use SSO for authentication, extending the threat even to accounts used with cloud-based applications.
“This subdomain was vulnerable to a reflected cross-site scripting (XSS) vulnerability where a specific function in the deployed application failed to sanitize and filter the arbitrary input passed by the remote user as a part of an HTTP request,” Sood said. “As a result, the attacker could have executed JavaScript in the context of the application, thereby impacting the privacy and security of Salesforce users.”
To carry out a phishing attack, a hacker would need to create a popup mimicking the Salesforce login and remotely inject the JavaScript. From there, the victim would enter their legitimate Salesforce credentials that are then sent to the attacker’s web server.
Cross-site scripting attacks (XSS) happen when malicious script is injected into a Website or Web-based application, and is a perennial web application security issue on the OWASP Top 10 list. Generally, an attacker will inject malicious script into GET request or it’s included in dynamic content. Usually XSS is enabled because a Web app fails to validate the input.
Source:https://threatpost.com
Lenovo used shady ‘rootkit’ tactic to quietly reinstall unwanted software
Lenovo has been caught using a technique, often used by some malware to withstand being deleted, to reinstall unwanted software on the computers it sells.
As reported on a number of forums and news-sharing sites, some users have accused the computer maker of overwriting Windows files to ensure its own-brand software and tools were installed — even after a clean install of the operating system.
The issue was first reported as early as May, but was widely reported Tuesday.
The “rootkit”-style covert installer, dubbed the Lenovo Service Engine (LSE), works by installing an additional program that updates drivers, firmware, and other pre-installed apps. The engine also “sends non-personally identifiable system data to Lenovo servers,” according to the company. The engine, which resides in the computer’s BIOS, replaces a core Windows system file with its own, allowing files to be downloaded once the device is connected to the internet.

But that service engine also put users at risk.
In a July 31 security bulletin, the company warned the engine could be exploited by hackers to install malware. The company issued a security update that removed the engine’s functionality, but users must install the patch manually.
Many Yoga and Flex machines (among others) running Windows 7, Windows 8, and Windows 8.1 are affected by the issue. Business machines, such as Think-branded PCs, are not affected.
A full list of affected notebooks and desktops is listed on Lenovo’s website.
It’s not the first time Lenovo has been caught in a privacy-related pickle.
Earlier this year, the computer maker was forced to admit it had installed Superfish adware over a three-month period on new machines sold through retail channels. The adware had the capability to intercept and hijack internet traffic flowing over secure connections, including online stores, banks, among others.
Users were told they should “not use their laptop for any kind of secure transactions until they are able to confirm [the adware] has been removed,” security researcher Marc Rogers told ZDNet at the time.
It was thought as many as 16 million consumers and bring-your-own-device users were affected by the preinstalled adware.
Source:http://www.zdnet.com/
Huge Flash Update Patches More Than 30 Vulnerabilities
Adobe has released a massive update for Flash, the application that has become the Internet’s problem child. The update contains patches for more than 30 vulnerabilities in Flash on Windows, OS X, and Linux.
Adobe pushed out the fixes on Tuesday afternoon, the latest in a long series of fixes for Flash in the last few weeks. The company has had to patch a number of vulnerabilities that were discovered in the cache of documents released after the Hacking Team hack. On July 7 Adobe fixed the first vulnerability in Flash used in Hacking Team’s Remote Control System intrusion platform. A week later the company patched two more bugs used by Hacking Team.

On Monday, researchers from Kaspersky Lab disclosed that attackers behind the Darkhotel APT campaign have been using one of the patched Flash bugs developed by Hacking Team in its attacks.
“Darkhotel seems to have burned through a pile of Flash zero-day and half-day exploits over the past few years, and it may have stockpiled more to perform precise attacks on high-level individuals globally,” Kaspersky Lab principal security researcher Kurt Baumgartner said.
The vulnerabilities Adobe patched Tuesday include a number of type confusion flaws, use-after-free vulnerabilities, buffer overflows, and memory corruption vulnerabilities. Many of the vulnerabilities can be used to take complete control of vulnerable machines.
Source:https://threatpost.com
Internet-Connected Gas Pumps Are a Lure for Hackers
IF ATTACKERS COULD cause a gas station’s tanks to overflow or prevent leak alarms from sounding, it could have devastating consequences—particularly if they struck multiple pumps in a region at once.
To see how real a threat that notion was, Kyle Wilhoit and Stephen Hilt from TrendMicro decided to set up a GasPot—a honeypot composed of virtual gas pump monitoring systems—to lure hackers and watch what they would do.
The work was inspired by Rapid7, which published a report earlier this year about finding 5,800 unsecured automated tank gauges accessible online. None of the systems—which belonged to gas stations, truck stops, and convenience stores primarily in the US—were password-protected.
Gas pump-monitoring systems vary in functionality, but they can include controls to set tank levels and overflow limits, monitor fuel-levels for inventory purposes and gauge the temperature of tanks. Some also detect leaks.

Remote attackers could take advantage of those controls in a few different ways. First, they could shut stations down by falsifying fuel levels to make it appear that tanks are low when they’re not, or they could change the “Unleaded” label on a tank to “Premium” or “Diesel,” causing confusion about inventory. They could also conceivably modify tank levels and overflow limits, potentially leading to dangerous spills. In 2009 in Puerto Rico, for example, a fuel tank exploded into flames and burned for three days after a computerized monitoring system failed to sense when the tank reached capacity during an automated refill.
The GasPot systems the researchers set up were designed to resemble Guardian AST (above-ground storage tank) monitoring systems made by Vedeer-Root. Guardian AST systems have been targeted in real-world attacks in the past by what appear to be hacktivists.
Hacking airport security systems with a common laptop
Hackers can compromise airport security networks by using a common laptop, this is the disconcerting discovery of the popular expert Billy Rios.
Cyber security from I-Team investigation revealed that hackers could have the ability to shut down an airport’s security network just using a laptop.
It is embarrassing read that system designed to improve security of the airports could represent the entry point for attackers.
“Walking by these devices and knowing how poorly secure they are, it doesn’t sit well with me,” explained the popular cyber security expert Billy Rios. “It’s pretty bad — probably no thought has been given to cyber security at all.”
In 2013, Billy Rios tested various machines deployed at airports throughout the world discovering numerous security vulnerabilities. The list of machines tested includes an X-ray scanner, an explosives detector, also known as itemiser, and a time clock.

Rios explained that the vulnerabilities affecting the machine could be exploited to access the airport’s network, for example, is discovered very common to discover hard-coded passwords into the software running on these security systems.
“So anyone that knew the username and password, which we know, could just log into the device and get access to an airport network,” said Rios. “It just takes one second to abuse some of the vulnerabilities that we’ve seen.”
The unauthorized access to an X-ray machine could be exploited by a terrorist or a criminal to hide weapons from screeners.
Rios reported the flaws to the US authorities that prompted the Department of Homeland Security to issue a warning about password vulnerabilities in some explosive detection machines. According to NBCNewYork , Rios has found many other flaws in the itemiser and in the time clocks.
“One machine Rios examined is called the itemiser. The company that makes itemisers says the version Rios bought was only used at foreign airports and the company recently released an update to correct the flaw, it said.
Rios maintains the broader concern continues at domestic airports, where he says he found three time clocks with vulnerable passwords.” states the NBCNewYork.
The company that produces the time clocks have already fixed the flaws and personnel at the airports can now change the passwords.
The most disconcerting aspect of the story is that it is likely that the vulnerabilities discovered by Rios have already been exploited, this is the opinion of the cyber security strategist from Cylance, Jon Miller.
“Now that we have extremists that are gaining these capabilities, they’re going to start using information for other types of attacks we haven’t seen before. It’s going to be a sobering couple of years,” said Miller.
The Cylance firm recently published a report on an Iranian hacking crew, which run a cyber espionage campaign exfiltrating sensitive information from many organizations and environments, including the airports.
“We were following them for 18 to 24 months, but it wasn’t until we started seeing them pull things like emergency response times and information that could put the physical safety of people at harm we knew we had to stop it,” says Miller.
“Anyone who has a copy of the plan on how an airport or any facility responds to an emergency now has a blueprint on how to beat that system,” said Kenneth Honig, a former commanding officer for the police department of the Port Authority of New York and New Jersey.
“Now that it’s been brought out into the open, hopefully they will take steps to fix it, but it will take time.” added Honig, who has 20 years leadership on the force.
Rios urges Transportation Security Administration to adopt more stringent requirements in term of cyber security of the equipment used in any airport.
“The bar is too low,” Rios said. “There will always be security issues, we can’t solve every single security issue, but we shouldn’t have the bar be so low that anybody can hack into these devices. The bar has to be a lot higher.”
Source:http://securityaffairs.co/
American Airlines, Sabre join growing number of China hacking targets
The companies appear to have been hacked by the same group that stole information from health insurer Anthem and the US government’s personnel office, according to a new report.
As if health insurance and government information weren’t enough, Chinese hackers may be targeting air travel — again.
American Airlines and Sabre, a company that processes airline reservations, may have been hacked by China-based hackers, Bloomberg reportedFriday, citing people who claim to have knowledge of the incidents. The companies are investigating the possibility of a security breach. It’s believed by Bloomberg’s sources that the same hackers who targeted health insurer Anthem and the US Office of Personnel Management (OPM) were behind the attacks. American Airlines, however, would not confirm that claim.
“American has worked with outside cyber security experts who checked digital signatures, IP addresses and style of attack and there’s no evidence to suggest a breach similar to that experienced by the U.S. Office of Personnel Management,” a company spokesman said in an e-mailed statement.

Still, the hackers’ purported attempts to make off with air travel information could have been part of a broader scheme to gather sensitive intelligence information on key individuals, and the attack on American Airlines was similar to those on OPM and Anthem, Bloomberg’s sources say. By attacking Anthem and the OPM, hackers could combine personal information about government employees, including medical history, with insights gleaned from air travel information, and track where those employees have been around the world and for how long. Ultimately, the hackers could use the information as a dossier to learn more about government officials and other Americans and perhaps use that to China’s advantage in espionage activities, the sources say.
The longtime battle with China
China has long been under suspicion for conducting successful cyberattacks on the US. While the government has claimed innocence in each attack, the US has charged China with actively targeting both companies and government institutions. One attack blamed on China attempted to intercept information on federal employees with top-secret security clearance in March 2014.
In May 2014, the US Justice Department filed charges against five alleged Chinese military hackers, claiming they infiltrated American corporations and stole information. China has denied the allegations and refuses to give up the individuals to US law enforcement agencies.
Meanwhile, the hacks continue. In June, the federal government confirmed that the OPM, the human resources arm of the federal government, was hacked and pointed to China-based hackers as the culprits. A month later, the US government said that over 21.5 million Social Security numbers and background checks from the OPM were stolen as part of the attack. That hack followed news in February that Anthem, the second-largest health insurer in the US, was hacked and saw the personal information of approximately 80 million members and employees accessed by the hackers.
Anthem CEO Joseph Swedish said the attack gave hackers access to names, dates of birth, member IDs, Social Security numbers and other personal information. Swedish said he found no evidence that any credit card or medical records had been exposed. The hacks have been unofficially tied to China, though Chinese officials have staunchly argued that they are not behind any attacks.
In addition to claiming innocence, China has fought back at the US, charging American spies with actively hacking and targeting its own networks and data. While the US has stayed tight-lipped on the matter, most security experts agree that the governments are indeed fighting a cyberwar behind the scenes.
The US is also in battle with other governments around the world. Russia, for instance, has been charged with breaching a White House network, which would have given it access to President Barack Obama’s schedule. North Korea has also reportedly attacked both government and company data and was charged last year with attacking Sony Pictures in an attempt to stop the controversial film, “The Interview,” from reaching theaters. The comedic film depicted an attempt by journalists to assassinate North Korea leader Kim Jong-un.
The US responds
In response to the many threats it faces, the US in April announced changes to existing policies that will make it easier for the government to respond to attacks.
US Defense Secretary Ash Carter outlined a new protocol in April that could see the US launch cyberattacks on foreign threats to either thwart or discourage cyberattacks on US government agencies and companies. That announcement followed an executive order signed by Obama in early April that will allow his cabinet to issue sanctions on foreign hackers. Like the Defense Department’s move, that tweak is aimed at stopping attacks before they happen.
“Effective incident response requires the ability to increase the costs and reduce the economic benefits from malicious cyber activity,” Lisa Monaco, assistant to the president for homeland security and counterterrorism, said in a statement at the time. “And this means, in addition to our existing tools, we need a capability to deter and impose costs on those responsible for significant harmful cyber activity where it really hurts — at their bottom line.”
United was also a target
The possible breach to American Airlines and Sabre would be the second airline-related attack reported in the past few weeks. Bloomberg reported July 29 thatUnited Airlines suffered a breach sometime this year that compromised customers’ flight records. The United hack reportedly came from the same China-based hackers who targeted the OPM and Anthem.
If the combined attacks are indeed a way for the Chinese government to triangulate government employee movements, hacking American Airlines, one of the largest US carriers and Sabre, would make sense. American Airlines had 52.2 million passenger boardings during the second quarter ended June 30. Sabre, which was spun off by American Airlines in 2000, says that it provides back-end technology to handle traveling reservations for 1 billion travelers each year. Together, the companies represent a treasure trove of information for anyone seeking ways to gather a full dossier on individuals.
Still, in addition to questions over who may have targeted the airline, it appears the attack may not have gotten as far as the hackers hoped. In an e-mailed statement, the American Airlines spokesman said that while the airline has brought in security experts, they have yet to discover any customer data breach.
“There is…no evidence that customer data may have been compromised,” the spokesman said. “We take cyber security very seriously and have a strong record of actively communicating with our customers and partners. We go above and beyond any notification requirements.”
A Sabre spokeswoman echoed American Airlines’ statement, saying that, while an investigation is ongoing, so far the company has not identified the theft of any personal information.
“Like most technology companies, Sabre experiences cyber security incidents,” the spokeswoman said in an e-mailed statement. “We recently learned of a cyber security incident, and we are conducting an investigation into it now. At this time, we are not aware that this incident has compromised sensitive protected information, such as credit card data or personally identifiable information, but our investigation is ongoing. We are committed to protecting sensitive information, and we are being assisted by experts that specialize in cyber security. We will share additional information as appropriate.”
The Chinese government did not respond to a request for comment.
Source:http://www.cnet.com/
“Funtenna” software hack turns a laser printer into a covert radio
LAS VEGAS—During the Cold War, Soviet spies were able to monitor the US Embassy in Moscow by using a radioretroreflector bug—a device powered, like modern RFID tags, by a directed radio signal. But that was too old school for Ang Cui, chief scientist at Red Balloon Security and a recent PhD graduate of Columbia University. He wanted to see if he could do all of that with software.
Building on a long history of research into TEMPEST emanations—the accidental radio signals given off by computing systems’ electrical components—Cui set out to create intentional radio signals that could be used as a carrier to broadcast data to an attacker even in situations where networks were “air-gapped” from the outside world. The result of the work of his research team is Funtenna, a software exploit he demonstrated at Black Hat today that can turn a device with embedded computing power into a radio-based backchannel to broadcast data to an attacker without using Wi-Fi, Bluetooth, or other known (and monitored) wireless communications channels.

Cui has previously demonstrated a number of ways to exploit embedded systems, including printers and voice-over-IP phones. In 2012, he demonstrated an exploit of Cisco phones that turned on the microphone and transformed phones into a remote listening device. Michael Ossmann of Great Scott Gadgets, a hardware hacker who has done some development of exploits based on concepts from the NSA’s surveillance “playset,” suggested to Cui that he could turn the handset cord of the phone into a “funtenna”—an improvised broadcast antenna generating radio frequency signals programmatically.
With just seven lines of code injected into the embedded computer of an otherwise unmodified laser printer, Cui was able to turn the printer into a radio transmitter by simply leveraging the electrical properties of existing input and output ports on the printer. By rapidly flipping the power state of general purpose input/output (GPIO) pins, Pulse Width Modulation (PWM) outputs, and UART (serial) outputs on a Pantum P2502W laser printer—“the cheapest laser printer we could find,” Cui said—the Funtenna hack was able to create a modulated radio signal as a result of the magnetic fields created by the voltage and resulting electromagnetic waves.
The hack couldn’t generate signals strong enough using the relatively short wires of the GPIO connections on the printer. Despite flipping every GPIO output available, he only got an effective range of transmission of a few meters. Instead, the UART output with a 10-foot cable generated a signal that could be picked up from outside a building—even through reinforced concrete based on Cui’s research.
The demonstration, Cui said, shows that embedded devices need their own built-in defenses to truly be secure. And printers are merely a starting point for Cui’s work. The same sort of attack could conceivably be launched from any “internet of things” device or other system with onboard computing power—including network routers and firewalls.
“A network [intrusion detection system] is no substitute for host-based defense,” he said. “You could monitor every known spectrum, but it would be very expensive and may not work. The best way is to have host-based defense baked into every embedded device.”
Source:http://arstechnica.com/